Assessment Description :-
You are to provide a security architectural design for a new, internet-based bank that you are setting up having been granted a banking license under the new No More Squirrelling legislation recently passed by the Federal Government.
ITNET202A Enterprise Security Assignment

Unit :- ITNET202A Enterprise Security
Assessment :- Type Report
Assessment Number :- 2
Assessment Weighting :- Case Study 40%
The requirements for this design are described below.
Because you are dealing with a bank a number of security concerns at various levels need to be addressed in your architecture :
1. Compliance with federal and state legislation
2.Public confidence in your enterprise by providing confidentiality, availability and integrity of customer data,
3.Privacy of customer data,
4.Interoperation with other financial institutions, both nationally and internationally,
5. Compliance with international standards,
6.Security of all bank assets,
7.Current trends in customer engagement via the internet
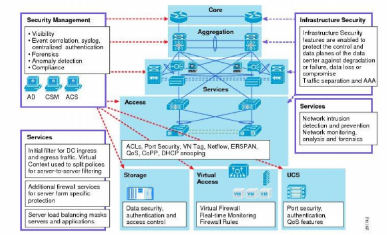
Your design needs to deal with enterprise architectural issues relating to application security plat form/OS security network security and storage security.
The decision has been made to run the bank’s IT operations in a Cloud environment.
B. Components you need to deliver:
1. I suggest that you use reference architectures if you can find these. The purpose of this work product is to show what types of security services you intend to provide what types of cloud services you will be using private public hybrid SaaS, PaaS, IaaS what types of systems and networking you will need for the bank consider head and branch office systems and networks, ATM and EFTPOS systems and
You will need to make reasonable assumptions about sizing capacity etc. of the various IT components and you need provide a design for best security practice i.e. cost is less of an issue than having security exposures and weaknesses.
2.Detailed logical level security architecture. This will include specific details of what security services you will provide, what networking you will provide what application systems you will be protecting what tools you will be using.
3.Detailed design physical level of your main processing site(s) irrespective of use of Cloud. This will include location security equipment networking devices storage sizing management tools operational components for the detailed security architecture.
4.Costing estimates (both labor, hardware and software, both for implementation and operation)
5.Planning estimates with enough detail to show estimates at equipment installation level
6.Resourcing estimates
7.Description of the security services you are planning to provide, why, and where they will be located in relation to the bank’s IT systems and networks.
8.Equipment lists describing what equipment you will be implementing to provide these security services.
For these latter components you would benefit from using the SABSA Framework for Security Service Management.
C. Approach:
Use the SABSA frame work as a guide for your work products Concentrate on the How Who and Where Process People and Location columns. You will have to do some research about how an organization like a bank would be running its IT systems and what they would consist of.
Detailed Submission Requirements
- Submission must be between 3500 – 4000 words (excluding references)
- All students submit the assessment through the Assessment Turnitin link on Moodle page for this unit.
Misconduct
- The assessment will be submitted through Turnitin via your unit page on Moodle.
- Turnitin is plagiarism software, which will identify if you have copied information and included it in your assessment.
- Copying information from others (i.e. websites, partner company information, or other students etc.) without the acknowledging the author is classified as misconduct.
- Engaging someone else to write any part of your assessment for you outside of the group work arrangement is classified as misconduct.
- To avoid being charged with Misconduct, students need to submit their own work and apply APA or Harvard Style Referencing (ask your lecturer
- The TAFE misconduct policy and procedure can be read on the TAFE
- Use the TAFE referencing guide accessible on Moodle.
ITNET202A Enterprise Security Assignment
Special consideration
- Students whose ability to submit or attend an assessment item is affected by sickness, misadventure or other circumstances beyond their control, may be eligible for special consideration. No consideration is given when the condition or event is unrelated to the student’s performance in a component of the assessment, or when it is considered not to be serious.
- Students applying for special consideration must submit the form within 3 days of the due date of the assessment item or exam.
- The form can be obtained from the TAFE
- The request form must be submitted to Admin Office. Supporting evidence should be attached. For further information please refer to the Student Assessment Policy and associated Procedure available on
ORDER This ITNET202A Enterprise Security Assignment NOW And Get Instant Discount
Read More :